Likelihood Estimation
The "Likelihood estimation" method is an alternative to the "Attack potential" method used for the attack feasibility evaluation. It determines AFR without building attack trees. Instead of using such trees, the initial and residual likelihood is estimated and translated into the AFR, as shown in the table below. The likelihood is divided into four categories: highly likely, likely, less likely, and unlikely.
|
AFR |
Likelihood |
| high | highly likely |
| medium | likely |
| low | less likely |
| very low | unlikely |
As a consequence, this method is far less rigorous and detailed and should therefore only be used in certain use cases, e.g., high-level TARAs, SW-only projects, projects with unclear context (which HW is used, which signals are transferred, which data is stored, etc.).
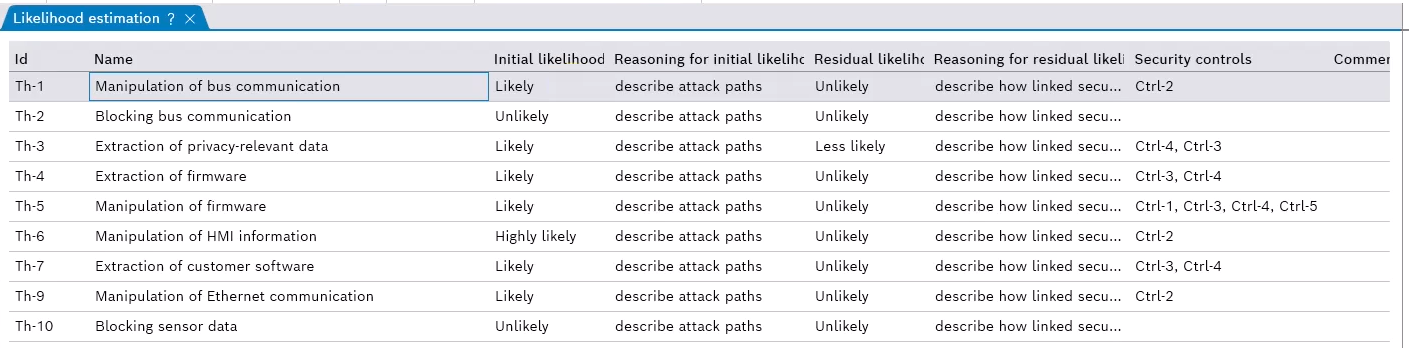
You can select this method while creating a new project. On the likelihood estimation page, each threat is rated with an initial likelihood, and the reasoning for the rating is given.
- If only a TARA is done, all other columns will stay empty.
- If RRA is conducted, the residual likelihood is rated based on the linked security controls. Furthermore, reasoning for the residual likelihood is mandatory.
To differentiate the Likelihood estimation from the Attack potential method
The main differences to the attack potential method are:
- The "Assumptions" can not be enabled or disabled.
- The "Security controls" can not be enabled or disabled.
- The "Likelihood method" page removes the attack trees, technical attack trees, circumvent trees, and attack leaves tabs from the Attack potential method.