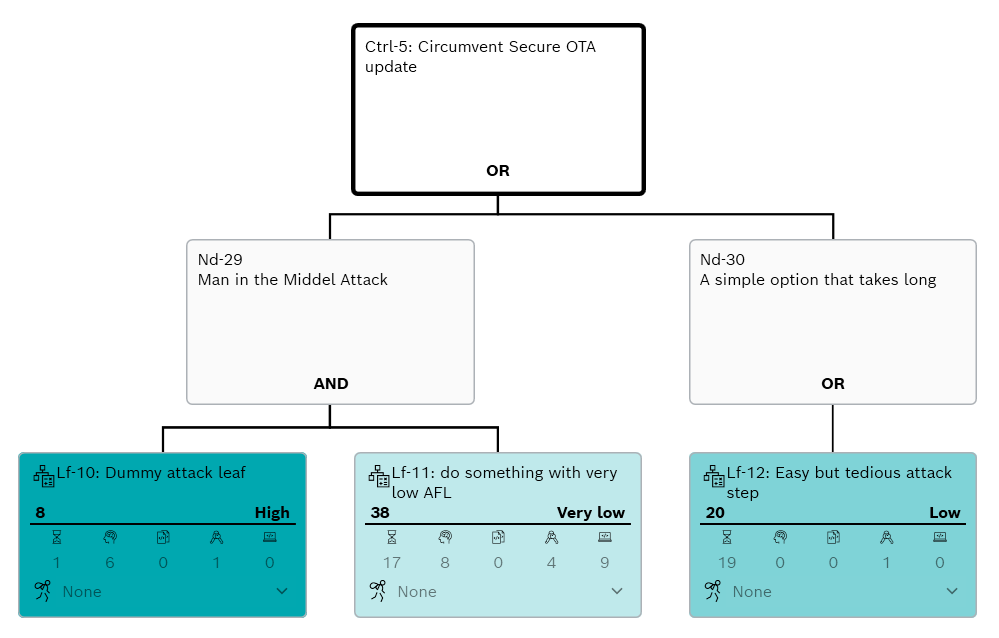
Circumvent Trees
A circumvent tree corresponding to a given security control is an attack tree where the root node is the action of circumventing the security control.
A circumvent tree models the actions required to circumvent its corresponding security control. It is referenced in attack trees and technical attack trees to indicate where an enabled security control must be circumvented. Hence, this is relevant only when security controls are assumed to be enabled, particularly for the residual risk analysis.