Attack Trees
An attack tree describes a set of attack paths that realize a given threat.
The goal of compiling an attack tree for a given threat is to systematically collect all possible and relevant attacks realizing that threat, i.e. achieving the attack goal described by the threat. For this purpose, the overall attack goal is broken down into sub-goals, and ultimately into elementary actions that must be performed in order to reach the goal.
An attack tree provides a structured way to compute the attack feasibility rating of a threat. Precisely one attack tree is designed for each threat. The nodes represent different actions that must be performed in order to carry out the attack and thus reach the attack goal.
Formally, an attack tree is a rooted tree (in the terminology of graph theory). The root node is the threat itself (recall that a threat is formulated as an action). Now consider any given node that has children. The action described by this node is decomposed into different steps and specified in more detail by the child nodes. Iterating this principle and decomposing each action further as we move away from the root, we see that the nodes describe more and more low level and elementary actions. Decomposition of a node stops when the author of the TARA decides that the node describes an action which is elementary and low level enough to be rated with an attack potential tuple; such a node is called a leaf.
In principle, an attack tree can have arbitrary depth, as the author deems appropriate, but as a general rule of thumb, three to five levels are often sufficient.
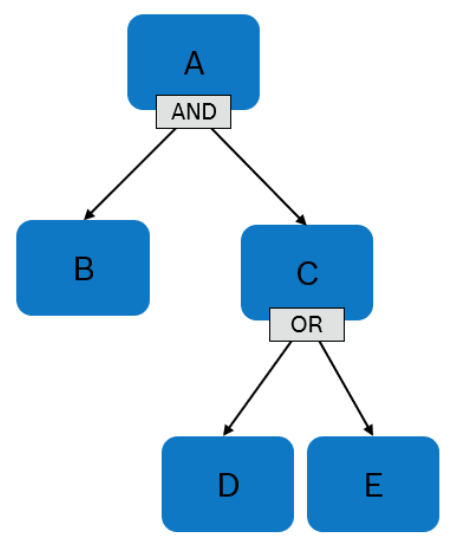
Any node that has children must be labeled either AND or OR.
- If a node is labeled AND, an attacker can perform the associated action by carrying out all actions described by its children.
- If a node is labeled OR, an attacker can perform the associated action by carrying out one of the actions described by its children.
Since all nodes that are not leaves are labeled either AND or OR, the attack tree describes a collection of attack paths, i.e., sets of elementary actions that can be carried out by an attacker in order to perform the action described by the root node (and the corresponding threat).